Modern enterprises depend on a complex mesh of SaaS tools, observability agents, and data pipelines. Each integration, whether a cloud analytics SDK, IoT telemetry feed, or on–prem collector, can become a hidden entry point for attackers. In fact, recent incidents show that breaches often begin outside core systems. For example, OpenAI’s November 2025 disclosure revealed that a breach of their third party analytics vendor Mixpanel exposed customers’ names, emails and metadata. This incident wasn’t due to a flaw in OpenAI’s code at all, but to the telemetry infrastructure around it. In an age of hyperconnected services, traditional security perimeters don’t account for these “data backdoors.” The alarm bells are loud, and we urgently need to rethink supply chain security from the data layer outwards.
Why Traditional Vendor Risk Management Falls Short
Most organizations still rely on point-in-time vendor assessments and checklists. But this static approach can’t keep up with a fluid, interconnected stack. In fact, SecurityScorecard found that 88% of CISOs are concerned about supply chain cyber risk, yet many still depend on passive compliance questionnaires. As GAN Integrity notes, “historically, vendor security reviews have taken the form of long form questionnaires, manually reviewed and updated once per year.” By the time those reports are in hand, the digital environment has already shifted. Attackers exploit this lag: while defenders secure every connection, attackers “need only exploit a single vulnerability to gain access”.
Moreover, vendor programs often miss entire classes of risk. A logging agent or monitoring script installed in production seldom gets the same scrutiny as a software update, yet it has deep network access. Legacy vendor risk tools rarely monitor live data flows or telemetry health. They assume trusted integrations remain benign. This gap is dangerous: data pipelines often traverse cloud environments and cross organizational boundaries unseen. In practice, this means today’s “vendor ecosystem” is a dynamic attack surface that traditional methods simply weren’t designed to cover.
Supply Chain Breaches: Stats and Incidents
The scale of the problem is now clear. Industry data show supply chain attacks are becoming common, not rare. The 2025 Verizon Data Breach Investigations Report found that nearly 30% of breaches involved a third party, up sharply from the prior year. In a SecurityScorecard survey, over 70% of organizations reported at least one third party cybersecurity incident in the past year and 5% saw ten or more such incidents. In other words, it’s now normal for a large enterprise to deal with multiple vendor-related breaches per year.
Highprofile cases make the point vividly. Classic examples like the 2013 Target breach (via an HVAC vendor) and 2020 SolarWinds attack demonstrate how a single compromised partner can unleash devastation. More recently, attackers trojanized a trusted desktop app in 2023: a rogue update to the 3CX telecommunications software silently delivered malware to thousands of companies. In parallel, the MOVEit Transfer breach of 2023 exploited a zero-day in a file transfer service, exposing data at over 2,500 organizations worldwide. Even web analytics are not safe: 2023’s Magecart attacks injected malicious scripts into ecommerce payment flows, skimming card data from sites like Ticketmaster and British Airways. These incidents show that trusted data pipelines and integrations are attractive targets, and that compromises can cascade through many organizations.
Taken together, the data and stories tell us: supply chain breaches are systemic. A small number of shared platforms underpin thousands of companies. When those are breached, the fallout is widespread and rapid. Static vendor reviews and checklists clearly aren’t enough.
Telemetry Pipelines as an Attack Surface
The modern enterprise is drowning in telemetry: logs, metrics, traces, and events flowing continuously from servers, cloud services, IoT devices and business apps. This “data exhaust” is meant for monitoring and analysis, but its complexity and volume make it hard to control. Telemetry streams are typically high volume, heterogeneous, and loosely governed. Importantly, they often carry sensitive material: API keys, session tokens, user IDs and even plaintext passwords can slip into logs. Because of this, a compromised observability agent or analytics SDK can give attackers unintended visibility or access into the network.
Without strict segmentation, these pipelines become free-for-all highways. Each new integration (such as installing a SaaS logging agent or opening a firewall for an APM tool) expands the attack surface. As SecurityScorecard puts it, every vendor relationship “expands the potential attack surface”. Attackers exploit this asymmetry: defending hundreds of telemetry connectors is hard, but an attacker needs only one weak link. If a cloud logging service is misconfigured or a certificate is expired, an adversary could feed malicious data or exfiltrate sensitive logs unnoticed. Even worse, an infiltrated telemetry node can act as a beachhead: from a log agent living on a server, an attacker might move laterally into the production network if there are no micro-segmentation controls.
In short, modern telemetry pipelines can greatly amplify risk if not tightly governed. They are essentially hidden corridors through which attackers can slip. Security teams often treat telemetry as “noise,” but adversaries know it contains a wealth of context and credentials. The moment a telemetry link goes unchecked, it may become a conduit for data breaches.
Securing Telemetry with a Security Data Fabric
To counter these risks, organizations are turning to the concept of a security data fabric. Rather than an adhoc tangle of streams, a data fabric treats telemetry collection and distribution as a controlled, policy-driven network. In practice, this means inserting intelligence and governance at the edges and in - flight, rather than only at final destinations. A well implemented security data fabric can reduce supply chain risk in several ways:
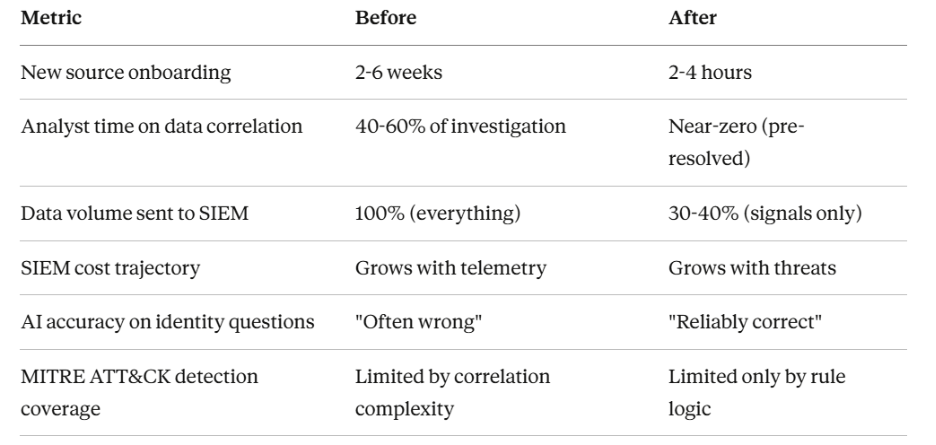
- Visibility into third - party data flows. The fabric provides full data lineage, showing exactly which events come from which sources. Every log or metric is tagged and tracked from its origin (e.g. “AWS CloudTrail from Account A”) to its destination (e.g. “SIEM”), so nothing is blind. In fact, leading security data fabrics offer full lifecycle visibility, with “silent device” alerts when an expected source stops sending data. This means you’ll immediately notice if a trusted telemetry feed goes dark (possibly due to an attacker disabling it) or if an unknown source appears.
- Policy - driven segmentation of telemetry pipelines. Instead of a flat network where all logs mix together, a fabric enforces routing rules at the collection layer. For example, telemetry from Vendor X’s devices can be automatically isolated to a dedicated stream. DataBahn’s architecture, for instance, allows “policy-driven routing” so teams can choose that data goes only to approved sinks. This micro-segmentation ensures that even if one channel is compromised, it cannot leak data into unrelated systems. In effect, each integration is boxed to its own lane unless explicitly allowed, breaking the flat trust model.
- Real-time masking and filtering at collection. Because the fabric processes data at the edge, it can scrub or redact sensitive content before it spreads. Inline filtering rules can drop credentials, anonymize PII, or suppress noisy events in real time. The goal is to “collect smarter” by shedding high risk data as early as possible. For instance, a context-aware policy might drop repetitive health - check pings while still preserving anomaly signals. Similarly, built -in “sensitive data detection” can tag and redact fields like account IDs or tokens on the fly. By the time data reaches the central tools, it’s already compliance safe, meaning a breach of the pipeline itself exposes far less.
- Alerting on silent or anomalous telemetry. The fabric continuously monitors its own health and pipelines. If a particular log source stops reporting (a “silent integration”), or if volumes suddenly spike, security teams are alerted immediately. Capabilities like schema drift tracking and real-time health metrics detect when an expected data source is missing or behaving oddly. This matters because attackers will sometimes try to exfiltrate data by quietly rerouting streams; a security data fabric won’t miss that. By treating telemetry streams as security assets to be monitored, the fabric effectively adds an extra layer of detection.
Together, these capabilities transform telemetry from a liability into a defense asset. By making data flows transparent and enforceable, a security data fabric closes many of the gaps that attackers have exploited in recent breaches. Crucially, all these measures are invisible to developers: services send their telemetry as usual, but the fabric ensures it is tagged, filtered and routed correctly behind the scenes.
Actionable Takeaways: Locking Down Telemetry
In a hyperconnected architecture, securing data supply chains requires both visibility and control over every byte in motion. Here are key steps for organizations:
- Inventory your telemetry. Map out every logging and monitoring integration, including cloud services, SaaS tools, IoT streams, etc. Know which teams and vendors publish data into your systems, and where that data goes.
- Segment and policy-enforce every flow. Use firewalls, VPC rules or pipeline policies to isolate telemetry channels. Apply the principle of least privilege: e.g., only allow the marketing analytics service to send logs to its own analytics tool, not into the corporate data lake.
- Filter and redact early. Wherever data is collected (at agents or brokers), enforce masking rules. Drop unnecessary fields or PII at the source. This minimizes what an attacker can steal from a compromised pipeline.
- Monitor pipeline health continuously. Implement tooling or services that alert on anomalies in data collection (silence, surges, schema changes). Treat each data integration as a critical component in your security posture.
The rise in supply chain incidents shows that defenders must treat telemetry as a first-class security domain, not just an operational convenience. By adopting a fabric mindset, one that embeds security, governance and observability into the data infrastructure, enterprises can dramatically shrink the attack surface of their connected environment. In other words, the next time you build a new data pipeline, design it as a zero-trust corridor: assume nothing and verify everything. This shift turns sprawling telemetry into a well-guarded supply chain, rather than leaving it an open backdoor.






.png)
.png)







.avif)

.avif)








